Monolith to Microservices: Implementing the Strangler Fig Pattern for Legacy Migration
A comprehensive guide on implementing the Strangler Fig Pattern for incremental monolith to microservices migration, including API facades and risk management strategies.
Drake Nguyen
Founder · System Architect
Introduction to the Strangler Fig Pattern
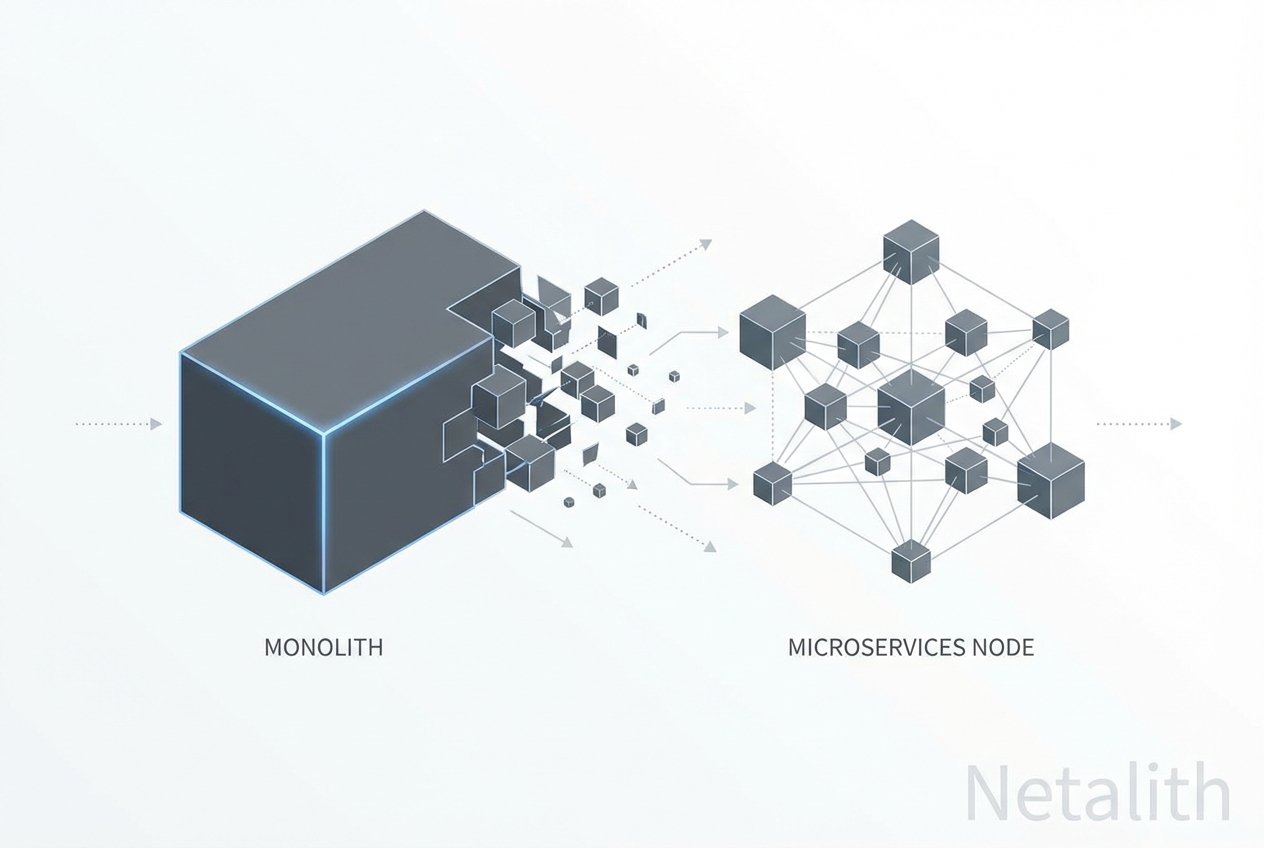
Modern enterprise software architecture requires unprecedented agility to keep pace with market demands. For organizations burdened by monolithic systems, a complete system rewrite often spells disaster. The most proven and effective methodology to achieve this transition safely is the strangler fig pattern.
Originating from the biological phenomenon where a strangler fig grows around a host tree until the host eventually dies, this approach offers a highly controlled legacy migration strategy. Instead of taking down the entire system at once, development teams build new microservices around the edges of the existing monolith. Over time, functionality is seamlessly routed to the new services, enabling a smooth migration path without disrupting ongoing business operations.
"The strangler fig pattern allows you to slowly replace a monolithic system with a modern architecture, managing risk while delivering continuous value."
This method of legacy refactoring has become the gold standard for enterprises looking to break free from the constraints of outdated infrastructure while minimizing downtime and maximizing modernization patterns.
Why Choose the Strangler Fig Pattern for Monolith Migration?
Embarking on a monolith migration can be a daunting, resource-intensive endeavor. The traditional "Big Bang" rewrite—where an entirely new system is built and swapped out overnight—carries catastrophic risks. This is why architects heavily prioritize the strangler bot pattern for modernization risk management.
By operating both the old and new systems simultaneously, organizations establish a robust coexistence strategy. This dual-run environment ensures that if a newly deployed microservice fails, the system can quickly roll back traffic to the monolith. Furthermore, the practice of incremental decommissioning ensures that legacy code is only retired once its modern counterpart has been fully tested and validated in production.
Evaluating Legacy System Modernization Strategies
When analyzing legacy system modernization strategies, technology leaders must compare various approaches. While some teams might opt for lift-and-shift cloud deployments, this doesn't resolve underlying architectural bottlenecks. True modernization requires meticulous service decomposition, breaking domain capabilities into bounded contexts that can be scaled and maintained independently as part of a comprehensive strangler pattern.
Incremental Migration to Microservices Tutorial: Step-by-Step
Transitioning from a tightly coupled architecture to distributed services requires careful planning. In this incremental migration to microservices tutorial, we outline a structured approach to utilizing the strangler bot pattern for migrating monoliths to microservices. By following this incremental rewrite pattern, teams can establish a reliable and repeatable migration path.
Implementing the API Facade Pattern
The crucial first step in your migration is decoupling the client-facing applications from the underlying backend logic. This is achieved by implementing an api facade pattern. An API gateway sits in front of your legacy system, acting as a single entry point for all client requests.
Initially, this gateway simply forwards 100% of the traffic to the monolith. However, as new services are built, the facade dynamically routes traffic based on the requested domain or endpoint. This is foundational to modern interception layer patterns.
Establishing the Interception Layer
To safely direct traffic, an interception layer must be configured at the routing level. Below is an example of how an interception layer routes traffic between the monolith and new microservices using standard gateway configurations:
// Conceptual Routing Configuration for the Interception Layer
location /api/v1/orders {
// Legacy traffic routed to monolith
proxy_pass http://monolith-backend;
}
location /api/v2/inventory {
// Modernized domain routed to new microservice
proxy_pass http://microservice-inventory;
}
Refactoring Monolithic Applications into Cloud-Native Architectures
Successfully refactoring monolithic applications into cloud-native environments requires more than just new infrastructure; it demands a shift in data management and domain modeling. Sometimes referred to as the strangler bot pattern in automated legacy migration communities, this process systematically chips away at the monolith's core.
During service decomposition and legacy refactoring, data coupling is often the hardest challenge. You must decouple databases alongside the application code. As you adopt cloud-native architecture patterns, you will likely need to explore distributed transaction solutions. We highly recommend reviewing the saga pattern vs event sourcing debate to determine how your new services will handle eventual consistency. Additionally, reading a comprehensive CQRS implementation guide can help you separate read and write models, preventing performance bottlenecks in your new microservices.
Overcoming Common Migration Challenges and Risk Management
Even with a sound coexistence strategy, challenges will arise. Effective modernization risk management involves anticipating data synchronization issues and network latency introduced by distributed systems.
- Data Synchronization: Because incremental decommissioning means both systems run concurrently, databases must be kept in sync using techniques like Change Data Capture (CDC).
- Network Latency: Moving from in-memory calls to network-based API calls increases latency. Applying appropriate resilience patterns in microservices (like circuit breakers and retries) is non-negotiable.
- Complexity: Distributed systems design inherently brings operational complexity. Implementing distributed tracing and robust logging early in the migration is critical to maintaining visibility across the hybrid architecture.
Frequently Asked Questions
What is the Strangler Fig Pattern in software architecture?
It is an architectural pattern used to incrementally migrate a legacy system by gradually replacing specific pieces of functionality with new applications and services, eventually "strangling" the old system until it can be safely decommissioned.
How does the Strangler Fig Pattern reduce modernization risk?
It mitigates risk by allowing teams to deploy small, isolated changes to production. Because both the old and new systems run simultaneously behind a routing layer, if a new service fails, traffic can be instantly reverted back to the legacy system.
What is the difference between the Strangler Fig Pattern and a Big Bang rewrite?
A Big Bang rewrite attempts to replace the entire legacy system at once, requiring a massive switchover event that is highly prone to failure. The strangler bot pattern, conversely, is an iterative approach that delivers value continuously and reduces deployment risks.
When should you NOT use the Strangler Fig Pattern?
You should avoid this pattern if the legacy system is small, inherently simple, or rarely updated. In such cases, the overhead of setting up an interception layer and dual-running systems may exceed the benefits of an incremental approach.
Conclusion: Embracing the Strangler Fig Pattern with Netalith
Transitioning from a monolith to microservices is a journey, not a single event. By adopting the strangler fig pattern, organizations can modernize their infrastructure at a sustainable pace, ensuring business continuity while embracing cloud-native architecture patterns. At Netalith, we specialize in helping enterprises navigate this complex migration path, providing the expertise needed to turn legacy burdens into scalable, distributed assets. Whether you are implementing the strangler pattern for the first time or refining your modernization risk management strategy, focus on incremental value and architectural resilience for long-term success.