Kali Linux file system guide: Understanding the Kali Linux File System Hierarchy: A Complete Guide
A technical guide to the Kali Linux directory structure, explaining the File Hierarchy Standard (FHS), root permissions, and where to find security tools.
Drake Nguyen
Founder · System Architect
Introduction to the Kali Linux File System Guide
Whether you are diving into penetration testing basics, preparing for a certification, or setting up a Kali Linux virtual machine for the first time, knowing where things are is half the battle. Welcome to the ultimate Kali Linux file system guide. For newcomers migrating from Windows or macOS, the Linux directory tree can initially feel like an impenetrable maze. However, mastering this environment is essential for anyone serious about modern ethical hacking.
This comprehensive Kali Linux architecture tutorial is designed to provide clear system file management Kali Linux strategies. We will focus on understanding Kali Linux file system hierarchy for beginners, ensuring you know exactly where your tools, scripts, and logs reside. By the time you finish this Kali Linux architecture tutorial, you will have a rock-solid Linux FHS overview and the confidence to navigate your hacking environment with precision.
What is the Linux File Hierarchy Standard (FHS)?
Before memorizing specific folder paths, it is critical to grasp the underlying rules of the operating system. The Linux File Hierarchy Standard (FHS) is the foundational blueprint that dictates how directories and files are organized. A clear Linux FHS overview is a mandatory step in understanding Linux directories.
Why does this matter? Because getting comfortable with the Linux directory structure explained for cybersecurity students guarantees that your knowledge will transfer to Debian, Ubuntu, and other enterprise Linux servers you might encounter during an engagement. The FHS ensures that essential Linux files for hackers—such as networking configurations, payload generators, and system logs—are placed in predictable, standardized locations. As you follow along with this Kali Linux architecture tutorial, you will see how heavily OffSec relies on these FHS principles to keep Kali efficient and organized.
Core Architecture: The Root Directory (/
The journey through the Kali directory structure begins at the very top: the root directory, represented by a single forward slash (/). In any Kali Linux architecture tutorial, the root directory structure must be highlighted as the parent of all other folders and files on your hard drive.
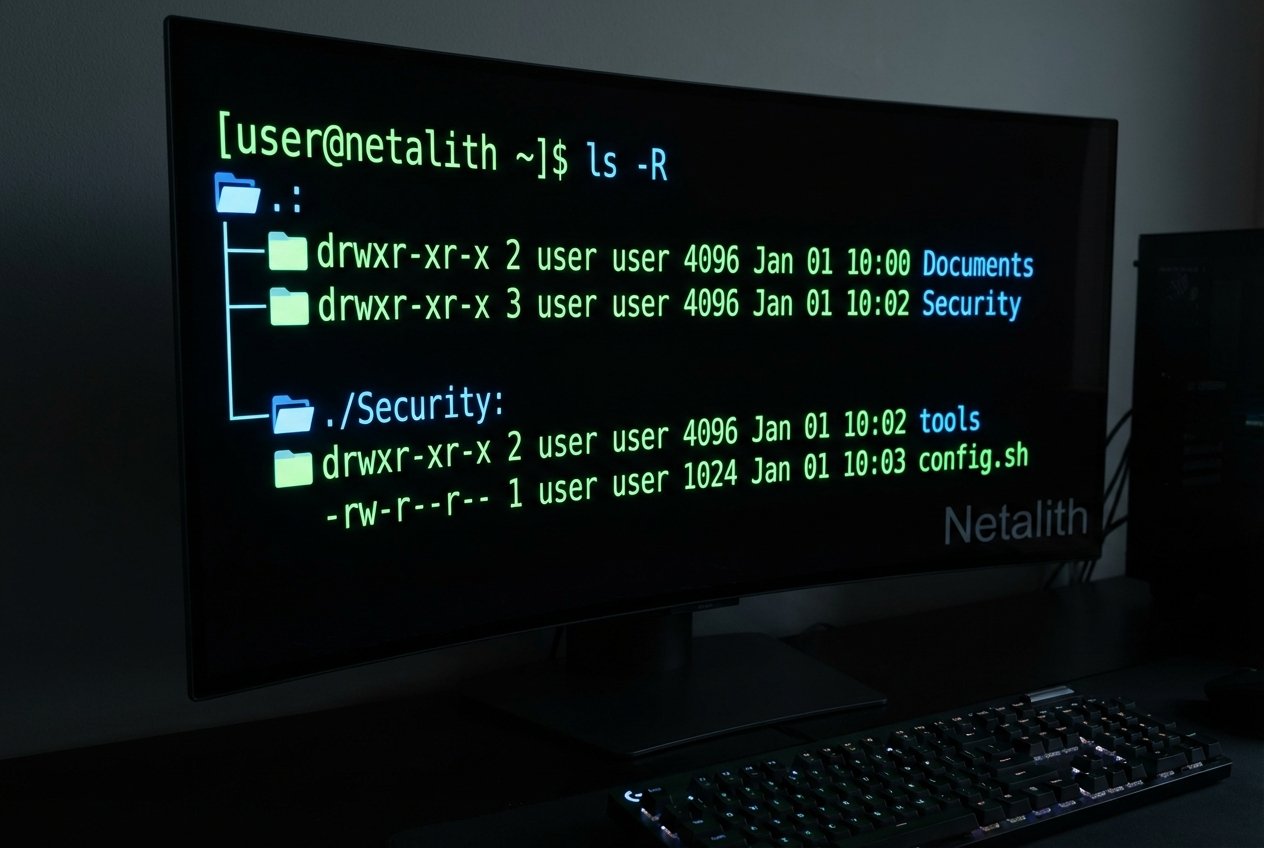
If you open your terminal and type ls -l /, you will see the foundational pillars of the OS. Proper root user permissions folders dictate that only the administrative user (root) can modify the core structure directly. Here is a simplified visual representation to help you in navigating Kali Linux folders guide parameters:
/
├── bin
├── boot
├── dev
├── etc
├── home
├── root
├── sbin
├── tmp
├── usr
└── var
Every directory branching off from / serves a highly specific purpose. Whether you are searching for device files in /dev or bootloader images in /boot, the root directory structure acts as the anchor point for your entire system.
Kali Linux /etc vs /var vs /usr Directories Explained
One of the most common stumbling blocks for newcomers is understanding the distinct roles of the /etc, /var, and /usr directories. This section of our Kali Linux architecture tutorial breaks down the Kali Linux /etc vs /var vs /usr directories explained for beginners, illustrating how system file management Kali Linux operates behind the scenes.
Binary File Directories: /bin and /sbin
While exploring the system, you will quickly encounter the primary binary file directories. The /bin directory houses essential user command binaries (like ls, cat, and ping) that are available to all users. In contrast, /sbin contains essential system binaries (like fdisk, iptables, and reboot) that generally require root privileges to execute. Understanding these binary file directories is vital when managing execution permissions or writing automated bash scripts.
Configuration File Locations: /etc
If you need to change how a service behaves, you head to the /etc directory. This is the central hub for configuration file locations. In Kali Linux, when you want to tweak your proxychains setup, alter your SSH daemon settings, or modify network interfaces, you will be editing text files within /etc. As a security professional, auditing these configuration file locations is also a prime tactic for privilege escalation and uncovering misconfigurations.
Temporary File Storage in Linux: /var and /tmp
System operations frequently generate data that changes or is only needed temporarily. The /var (variable) directory is where the system stores log files (/var/log), web server root folders (/var/www/html), and database files. Meanwhile, /tmp serves as a global scratchpad for temporary file storage Linux. The /tmp folder is notoriously useful during penetration tests because it typically features world-writable permissions, making it a frequent drop zone for exploit scripts.
Home Directory vs Root Directory in Kali
A point of frequent confusion in the Kali Linux folders guide is distinguishing between the standard user's home directory and the system's root directory. Let us clarify the home directory vs root directory Kali debate.
Historically, Kali Linux defaulted to a single "root" user. Today, for security reasons, the standard installation sets up a non-privileged user (usually named kali).
- The Home Directory (
/home/kali): This is your personal workspace. Represented by the tilde symbol (~), it is where your downloads, desktop files, and personal project folders live. You have full read, write, and execute permissions here without needingsudo. - The Root Directory (
/root): This is the specific home folder reserved for the absolute system administrator (the root user). Because it is part of the root user permissions folders, standard users cannot access/rootwithout elevating their privileges.
Throughout your cybersecurity journey and while studying this Kali Linux architecture tutorial, always remember to operate from your standard home directory and elevate to root only when necessary.
Where Are Tools Located in Kali Linux?
If you are looking for a where are tools located in Kali Linux architecture tutorial, you are likely looking for the actual penetration testing applications. So, where are all the Linux files for hackers kept?
In Kali Linux, the vast majority of pre-installed security tools are stored within the /usr directory hierarchy. Here is how they are mapped out:
/usr/bin: This is where most of the executable binaries for tools (likenmap,sqlmap, andgobuster) are located./usr/sbin: Security tools that strictly require administrative privileges to run are placed here./usr/share: This is perhaps the most important folder for hackers. It houses the read-only data, wordlists (like/usr/share/wordlists/rockyou.txt), Nmap scripts, Metasploit modules, and application resources.
If you are struggling with finding tool binaries in Kali Linux, you do not have to search manually. You can use the which or whereis commands in the terminal to quickly locate any utility.
Conclusion to Our Kali Linux File System Guide
Understanding the internal structure of your OS is what separates a script kiddie from a professional penetration tester. This Kali Linux file system guide has covered everything from the root directory structure to the specific configuration file locations found in /etc. By mastering navigating Kali Linux folders guide principles and the FHS, you ensure that your workflow remains efficient and your system management remains precise. Keep exploring the /usr/share and /var/log directories to deepen your knowledge of how Kali operates under the hood.