Micro-segmentation Strategies: Preventing Lateral Movement in Modern Cloud Environments
A comprehensive guide on micro-segmentation strategies to prevent lateral movement and secure modern cloud workloads through workload isolation and Zero Trust principles.
Drake Nguyen
Founder · System Architect
Introduction: The Urgent Need for Micro-segmentation in Hybrid Cloud
As enterprise cloud environments become increasingly complex and decentralized, the mandate for modern security is clearer than ever: organizations must assume breach. Once malicious actors bypass the traditional perimeter, a flat network architecture provides them with unfettered access to sensitive data and critical systems. To combat this, modern IT teams are prioritizing micro-segmentation as a foundational security measure.
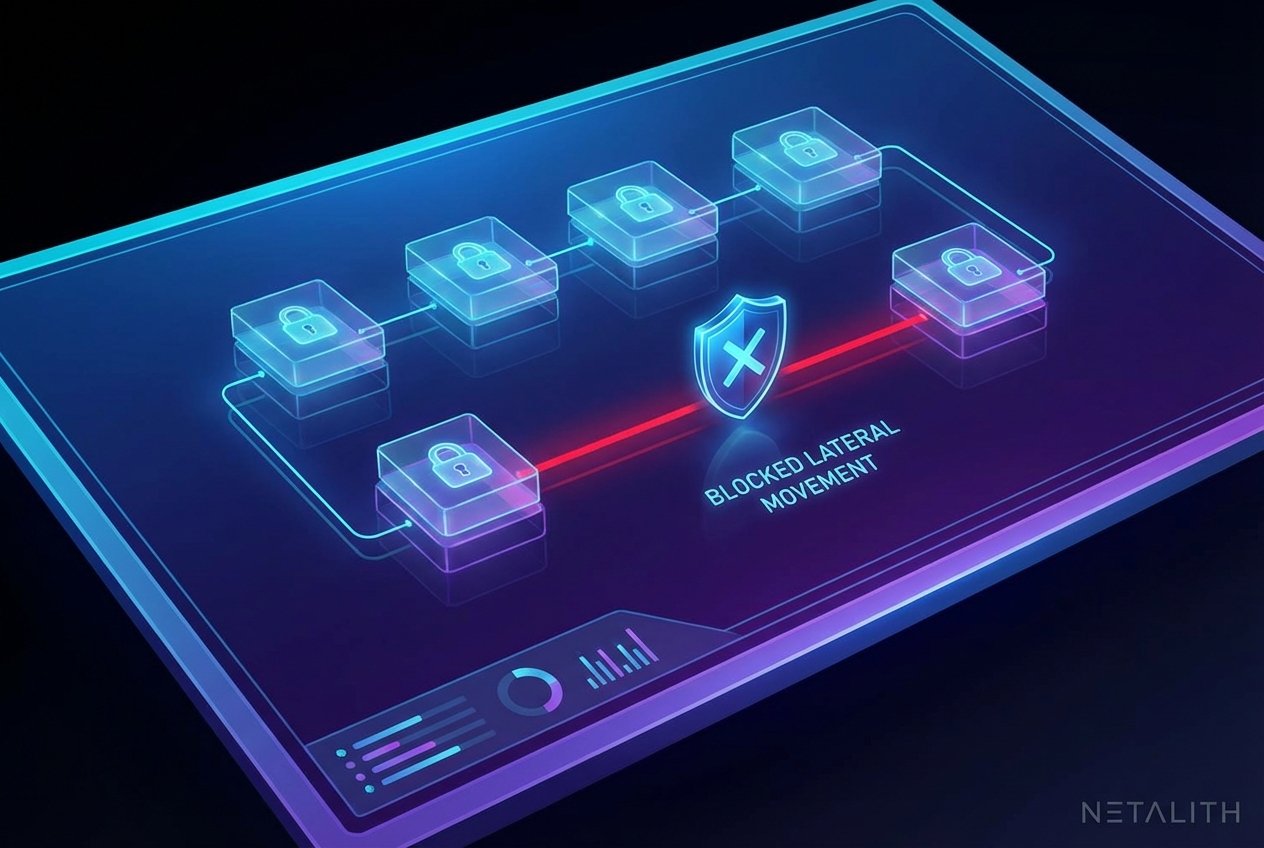
Effective cloud segmentation provides a vital defense mechanism by decoupling security controls from the physical network infrastructure. By enforcing strict workload isolation at the individual application or process level, organizations can drastically reduce their attack surface. Ultimately, lateral movement prevention is the primary goal; if a single server, container, or virtual machine is compromised, granular segmentation ensures the blast radius is tightly contained, neutralizing the threat before it can spread.
Micro-segmentation vs Traditional Network Segmentation
Understanding the critical shift in modern security requires analyzing granular segmentation vs traditional network segmentation. Historically, IT teams relied on macro-segmentation techniques—using VLANs, firewalls, and subnets—to divide the network into broad zones. While effective for managing north-south traffic (data entering and leaving the data center), this approach fails to secure the massive volume of communication occurring between internal systems.
Conversely, network microsegmentation represents a granular approach to segmentation. Instead of relying on static IP addresses or physical network topologies, it creates an internal perimeter security boundary around individual workloads, regardless of where they reside.
- Scope of Control: Traditional segmentation secures the perimeter; micro-segmentation secures the workload.
- Policy Granularity: Traditional methods use broad IP-based rules. Micro-segmentation employs granular segmentation based on application logic, identity, and environmental tags.
- Adaptability: In dynamic cloud environments, network microsegmentation automatically adapts to workload changes, whereas traditional firewalls require manual rule updates.
The Mechanics of Preventing Lateral Movement with Micro-segmentation Strategies
The core objective of any modern security architecture is limiting an attacker's ability to pivot within the environment. Preventing lateral movement with granular segmentation strategies involves a combination of deep visibility, automated policy enforcement, and dynamic access controls.
Because the vast majority of data center and cloud traffic operates laterally, east-west traffic monitoring is the crucial first step. By gaining comprehensive visibility into how applications communicate across the environment, security teams can define what constitutes legitimate traffic. Once baselines are established, a segmentation gateway or software-defined control plane can block all unauthorized communication pathways.
This process relies heavily on continuous verification. Rather than trusting a workload simply because it exists within the internal network, the system continuously verifies the workload's identity, health, and context before allowing it to communicate. By making lateral pathways invisible and inaccessible to unauthorized entities, lateral movement prevention becomes mathematically predictable rather than reliant on reactive threat detection.
Micro-segmentation Best Practices for Cloud Workloads
Deploying controls across highly dynamic, distributed environments requires a strategic approach. To ensure success, organizations should adhere to proven granular segmentation best practices for cloud workloads.
First, successful implementation demands comprehensive application dependency mapping. Before applying any restrictions, teams must visually map how workloads interact, identifying dependencies to avoid disrupting business-critical applications. Once traffic flows are mapped, security engineers can confidently draft granular security policies that explicitly allow required communications while denying everything else (a default-deny posture).
Next, policies must be rooted in the least privilege access principle. Every workload should be granted only the minimum network access necessary to perform its intended function. This ensures that even if a workload is compromised, its communication capabilities remain severely restricted, achieving optimal workload isolation.
How to Implement Micro-segmentation in AWS and Azure
For cloud architects, knowing how to implement granular segmentation in AWS and Azure is a highly sought-after skill. The approach in modern public clouds relies on decoupling security from IP addresses and attaching it directly to metadata and tags.
In both AWS and Azure, effective cloud segmentation begins with robust labeling conventions. By tagging workloads based on application tier, environment (e.g., production vs. staging), and regulatory compliance needs, security teams can apply dynamic rules. Implementing this effectively requires deep application dependency mapping across multi-cloud environments, ensuring that native tools (like AWS Security Groups or Azure Network Security Groups) or advanced third-party platforms apply consistent workload isolation policies without breaking communication flows.
Container Security and Workload Isolation
As microservices architectures dominate, container security segmentation has emerged as a distinct and urgent challenge. Containers are highly ephemeral—spinning up and spinning down in seconds—making traditional security controls entirely obsolete.
To achieve workload isolation in Kubernetes or Docker environments, organizations must utilize granular segmentation that operates at the orchestration layer. Security policies must follow the lifecycle of the container automatically. By embedding granular security policies directly into the CI/CD pipeline and the container orchestration plane, organizations can ensure that even short-lived microservices are instantly isolated upon deployment, preserving container security segmentation at scale.
Identity-Based Micro-segmentation in a Zero Trust Architecture
The future of cloud defense relies on identity-based granular segmentation. Unlike legacy systems that secure workloads based on network coordinates, this modern approach secures assets based on cryptographic identities. This methodology is the cornerstone of a mature Zero Trust Architecture (ZTA).
In identity-centric security models, communication is authenticated and authorized at the workload level before any network connection is established. This concept aligns perfectly with Zero Trust Network Access (ZTNA), extending the philosophy from human users to machine-to-machine communications. By tying policies to specific identities, identity-based segmentation ensures that workloads retain their security posture regardless of underlying network changes, IP reassignments, or cloud migrations.
Conclusion: Securing the Cloud with Netalith
In an era of persistent threats, micro-segmentation is no longer optional; it is a critical requirement for maintaining a resilient security posture. By shifting from broad network perimeters to granular, identity-based controls, organizations can effectively neutralize the risk of internal breaches. As you refine your cloud security strategy, leveraging a platform like Netalith ensures that lateral movement prevention and workload isolation are integrated seamlessly into your existing workflows. Embracing these advanced strategies will not only protect your sensitive data but also enable your organization to scale securely in an increasingly complex digital landscape.